Overview
With over 70% of all attacks now carried out over the web application level, organizations need every help they can get in making their systems secure.
Web application firewalls are deployed to establish an external security layer that increases the protection level, detects and prevents attacks before they reach web-based software programs.
ModSecurity is an open-source web-based firewall application (or WAF) supported by different web servers: Apache, Nginx and IIS.
Usage
The module is configured to protect web applications from various attacks. ModSecurity supports flexible rule engine to perform both simple and complex operations. It comes with a Core Rule Set (CRS) which has various rules for:
- cross website scripting
- bad user agents
- SQL injection
- trojans
- session hijacking
- other exploits
Most common errors
The most common error triggered by a mod_security rule on our shared servers is 403 Forbidden one:
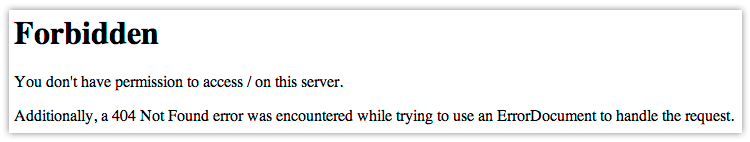
It simply states that you do not have permission to access / on the server. Depending on the exact link where you get the error, the path may vary.
ModSecurity works in the background, and every page request is being checked against various rules to filter out those requests which seem malicious. These can be the ones that have been run to exploit vulnerabilities in your website software with the only goal to hack the site.
Sometimes, due to poor website coding, mod_security may incorrectly determine that a certain request is malicious, while it is actually legitimate. When it happens, you still get a 403 error.
NOTE: Besides the 403 Forbidden error, you may also receive 404 Not Found or 500 Internal Server Error errors.
When to contact us
Once you have run into the issue with triggered by mod_security, the only way to bypass the block is to white-list this rule on the server.
Some simple steps to detect mod_security block are as follows:
- You get one of the specified errors on your website frontend or backend when performing certain actions/requests: 403 Forbidden, 500 Internal Server Error, 404 Not Found.
- The way to reproduce the error is usually the same all the time (as far as mod_security blocks a certain activity only).
- The other functionality on your website frontend/backend remains normal.
NOTE: If mod_security rules are triggered too often on your website(-s), the corresponding IP address (the one those requests are sent from) will be blocked by the server firewall. This will result in your cPanel account being completely unavailable from this IP.
ModSecurity rule(-s) may be whitelisted by our support team only. It is also possible to disable mod_security for the account in whole, but you should understand the risks once the specified module is off.
That's it!
Need any help? Contact our HelpDesk